In today’s interconnected world, manufacturers increasingly rely on digital solutions to streamline operations, increase efficiency, and stay competitive. However, with the benefits of digital transformation come new challenges, particularly in the realm of cybersecurity. Manufacturers need to safeguard their sensitive data and critical systems from a growing array of IT threats. This is where anspired, with its security-focused plans, steps in to protect manufacturing companies from IT threats. In this blog, we’ll explore how anspired’s security-focused approach is a game-changer for manufacturers.
Understanding the Stakes
Manufacturers are prime targets for cyberattacks due to the valuable data they store and the potential disruption they can cause. IT threats, including malware, ransomware, and data breaches, can result in substantial financial losses, operational disruptions, and damage to a manufacturer’s reputation. To tackle these threats head-on, anspired provides a comprehensive suite of security-focused plans designed to mitigate risk and enhance resilience.
Key Features of anspired’s Security-Focused Plans
- Proactive Threat Monitoring: anspired employs advanced threat monitoring tools to continuously scan your network and systems for signs of malicious activity. This proactive approach ensures that potential threats are identified and addressed before they can cause significant damage.
- Firewall and Intrusion Detection: anspired’s security plans include robust firewall solutions and intrusion detection systems to safeguard your network from unauthorized access and potential breaches. This critical layer of security helps to protect your sensitive data and proprietary information.
- Data Encryption: anspired’s plans include encryption measures to protect data both in transit and at rest. This means that even if unauthorized access occurs, the data is unintelligible to malicious actors, providing an additional layer of protection.
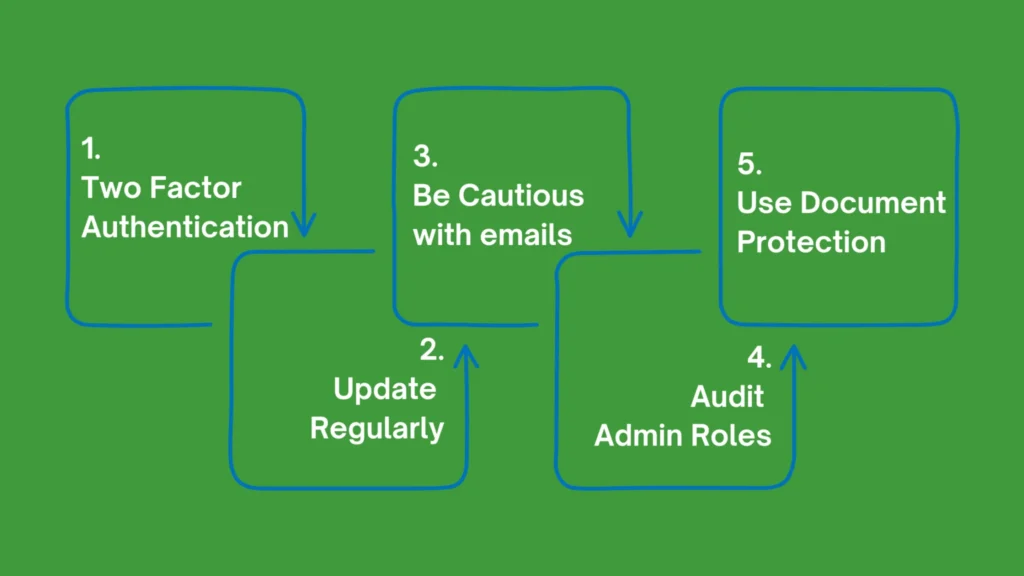
- Regular Updates and Patch Management: Manufacturers often rely on a variety of software and hardware components. anspired’s plans ensure that all systems and applications are kept up to date with the latest security patches, reducing vulnerabilities that attackers may exploit.
- Employee Training: Human error is a significant factor in many cybersecurity incidents. anspired’s security-focused plans include employee training to raise awareness about security best practices, including recognizing phishing attempts and adhering to password policies.
- Incident Response and Recovery: Despite robust security measures, breaches can still occur. anspired’s plans incorporate incident response and recovery strategies, enabling swift and effective action in the event of a security incident, minimizing damage and downtime.
Customised Solutions for Manufacturers
One of the standout features of anspired’s security-focused plans is their tailor-made approach. They recognize that each manufacturing client has unique needs and vulnerabilities. Whether you’re a small manufacturer with specific security concerns or a large-scale operation requiring a comprehensive security solution, anspired will work with you to create a customized plan that fits your specific requirements.
Conclusion
Manufacturers are at the forefront of digital innovation, but this also makes them prime targets for IT threats. anspired’s security-focused plans provide the vital protection manufacturers need in an increasingly digital world. By implementing proactive monitoring, robust firewall solutions, encryption measures, regular updates, employee training, and incident response strategies, anspired helps manufacturers stay resilient and secure.
In the fast-evolving landscape of IT threats, a security-focused approach is not just an option; it’s a necessity. With anspired as a partner, manufacturers can focus on their core business, confident that their digital assets are safeguarded against evolving IT threats.