With technology permeating every aspect of our lives, from personal communication to business operations, the protection of sensitive information and systems has become paramount. As a result, businesses face the challenge of how to safeguard their digital assets.
The answer to this pressing challenge lies in the realm of cyber security. By implementing robust cyber security measures, businesses can fortify their defences and mitigate the risks posed by cyber threats. Cyber security encompasses a comprehensive approach that includes proactive measures such as risk assessments, vulnerability scanning, and penetration testing, as well as reactive measures like incident response and recovery planning.
In this blog post, we will explore some frequently asked questions about cyber security, shedding light on its significance and providing essential insights to help you navigate the digital landscape securely.
So, why is Cyber Security so important?
Cyber security is crucial to a business for several key reasons.
It protects sensitive information, such as customer data and financial records, from unauthorised access and theft. By ensuring the confidentiality of this information, businesses can maintain trust with their customers and partners.
Cyber security safeguards a business’s reputation. A data breach or attack can result in significant damage to a company’s brand image and customer trust. By implementing effective cyber security measures, you can help mitigate financial losses associated with remediation, recovery, legal actions, and regulatory fines.
Robust Security protects against the constantly evolving threat landscape, allowing businesses to stay ahead of emerging threats and adapt to new attack vectors.

What are some common types of Cyber threats?
When it comes to cybersecurity, understanding the common types of cyber threats is essential for protecting yourself and your organisation. Here are some notable examples:
Malware: Malicious software, such as viruses, worms, trojans, ransomware, and spyware, is designed to infiltrate computer systems, steal sensitive information, or cause damage.
Phishing: Phishing attacks involve cybercriminals posing as trustworthy entities to deceive individuals into revealing sensitive information, like passwords or credit card details, through deceptive emails or websites.
Denial-of-Service (DoS) and Distributed Denial-of-Service (DDoS) Attacks: These attacks overload networks, servers, or websites with a flood of traffic, rendering them inaccessible to legitimate users.
Social Engineering: Cybercriminals exploit human psychology to manipulate individuals into sharing confidential information or granting unauthorised access. Tactics include impersonation, pretexting, baiting, or creating a sense of urgency.
SQL Injection: Attackers exploit vulnerabilities in web applications by injecting malicious SQL code, potentially gaining unauthorised access to databases, or manipulating data.
Man-in-the-Middle (MitM) Attacks: Cybercriminals intercept and alter communications between two parties, enabling them to eavesdrop, modify, or steal sensitive information transmitted over networks.
Password Attacks: Techniques like brute-force attacks or dictionary attacks are used to crack or guess passwords, providing unauthorised access to systems or accounts.
Zero-day Exploits: These attacks take advantage of previously unknown vulnerabilities in software or systems, leaving organisations vulnerable until the vulnerability is discovered and patched.
How Can Businesses Safeguard their Assets?
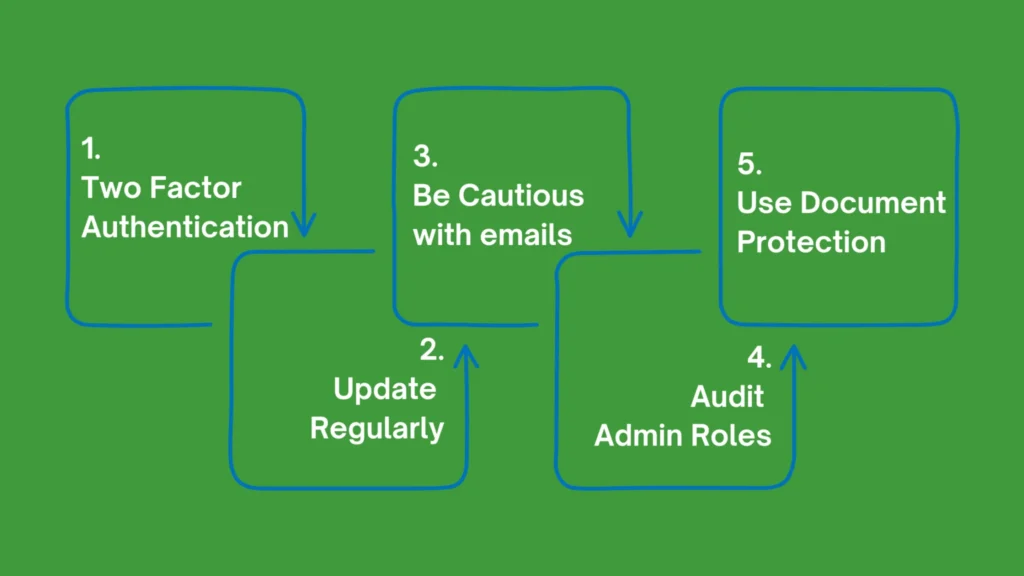
It’s quite simple..
As a business owner cyber security should be your utmost priority.
Underestimating the significance of a Managed Service Provider and their role as a fundamental pillar of success in your business would be a mistake.
What criteria should I consider when choosing a Managed Service Provider?
Evaluate their expertise and experience in providing managed services, specifically in the areas relevant to your business needs.
Assess the range of services offered and their ability to customise solutions to fit your requirements. Look for strong security technologies and tools, along with a proven incident response and management approach.
Consider their reputation, client references, and compliance expertise. Additionally, review their service level agreements and balance the cost with the value provided.
By carefully evaluating these criteria, you can choose an MSP that aligns with your business objectives and ensures reliable and effective managed services.
For more information about anspired, and the Managed Service we provide, visit our website at www.anspired.com.au.

What Role Does Artificial Intelligence (AI) Play in Cyber Security?
AI-powered systems can analyse vast amounts of data in real-time, identifying patterns, anomalies, and potential threats that may go unnoticed by traditional security measures.
Machine learning algorithms enable AI to learn from previous attacks and adapt its defenses accordingly, continuously improving its ability to detect and mitigate emerging threats.
AI also helps automate security processes, enabling faster response times and reducing the workload on human security professionals.
By harnessing the power of AI, organisations can strengthen their cybersecurity posture and stay one step ahead of cybercriminals.
In conclusion, cyber security is an indispensable aspect of modern business operations. Implementing robust measures, understanding common threats, and leveraging Artificial Intelligence can strengthen defenses and safeguard valuable assets in the ever-evolving digital landscape. Prioritising cyber security is not just a necessity, but a strategic imperative for organisations aiming to protect sensitive information, maintain trust, and stay ahead of emerging threats.
Are you in search of dependable Cyber Secuirty and IT Support?
Look no further than anspired, Australia’s #1 Protected Services Provider.
Contact us today to learn more.
www.anspired.com.au
1300 267 747.